AI Forensics | TryHackMe Write-up
Complete walkthrough for AI Forensics TryHackme room. Explore AI DFIR and learn how it boosts your investigation capabilities.
This is my write-up for the TryHackMe room on AI Forensics. Written in 2026, I hope this write-up helps others learn and practice cybersecurity.
Task 1: Introduction
This section introduces the scope of the room, outlining the prerequisites and learning objectives. It aims to explore the implementation of AI and ML in the Digital Forensics and Incident Response (DFIR) field, focusing on its potential benefits, daily application, and the ethical or legal implications that accompany it.
Learning Prerequisites
I'm ready to learn!
No answer needed
Task 2: The AI Forensics Landscape
This task highlights how AI and Machine Learning can solve significant DFIR challenges, such as handling massive data processing, detecting anomalies that human analysts might miss, and scaling effortlessly across modern infrastructures. It also emphasizes critical limitations of AI, including its probabilistic (non-deterministic) nature, the "Garbage In, Garbage Out" (GIGO) principle, and the need to balance accuracy, precision, and recall metrics.
What ability of AI helps turn a DFIR investigator by recognising patterns they might not have been able to comprehend?
Anomaly Detection
Which metric tells you the proportion of positively flagged results that were actually correct?
Precision
What term describes the AI characteristic where the same input may yield different outputs across different runs?
Non-determinism
Task 3: AI & DFIR
This section details practical implementations of AI across different forensic domains. It covers Convolutional Neural Networks (CNNs) and GANs for detecting image forgery and deepfakes, Transformer models (like BERT) for processing chat logs and detecting phishing emails, automated timeline reconstruction from fragmented data, and using deep neural networks for static and dynamic malware analysis.
What type of neural network is commonly used in image and video forensics due to its ability to learn spatial patterns in visual data?
Convolutional Neural Network
What kind of analysis can be performed on social media or chat logs to assess the emotional tone of messages?
Sentiment analysis
What type of data do AI systems correlate to reconstruct the timeline of an incident automatically?
Time-sequenced
What type of analysis observes how a program behaves to determine whether it is malicious, e.g., using its API call sequence?
Dynamic analysis
Task 4: AI Legal & Ethical Implications
This task examines the heavy legal and ethical responsibilities of using AI in the courtroom. It explores the "black box" problem where AI lacks explainability (risking failure of the Daubert test), algorithmic bias that can lead to unfair or racially skewed outcomes, the difficulty of maintaining a strict chain of custody, and the privacy issues associated with feeding sensitive evidence into public cloud AI models.
What legal test used in the U.S. assesses whether expert or scientific testimony is admissible in court?
Daubert
What term describes AI models whose internal decision-making processes are difficult to interpret?
Black box
What real-world technology used by law enforcement has been shown to produce racially biased results in identifying suspects?
Facial recognition
What technique allows machine learning to be performed without transferring sensitive data to a central server, helping preserve privacy?
Federated learning
Task 5: Practical - The Digital Trail
A hands-on lab scenario investigating a suspected network breach at a tech company named RobbCo. Using AI-enhanced Python scripts (classify_logs.py and file_anomalies.py), the investigator maps out the attack lifecycle: initial access via a phishing lure (invoice_Q1_2075.ods), privilege escalation using abused sudo permissions to plant SSH keys, disguise and persistence using a reverse shell masquerading as a monitoring tool (sysmon), and finally, the exfiltration of proprietary source code hidden in shared memory.
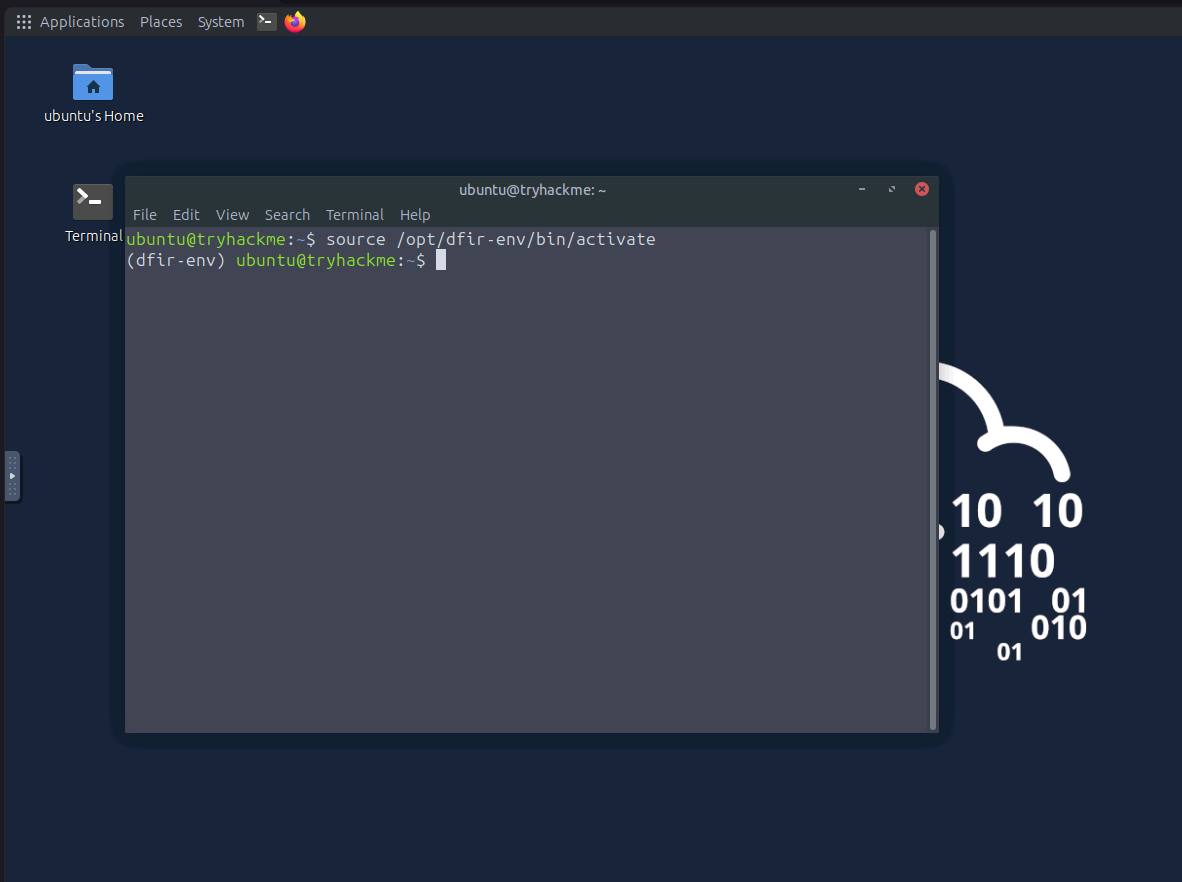
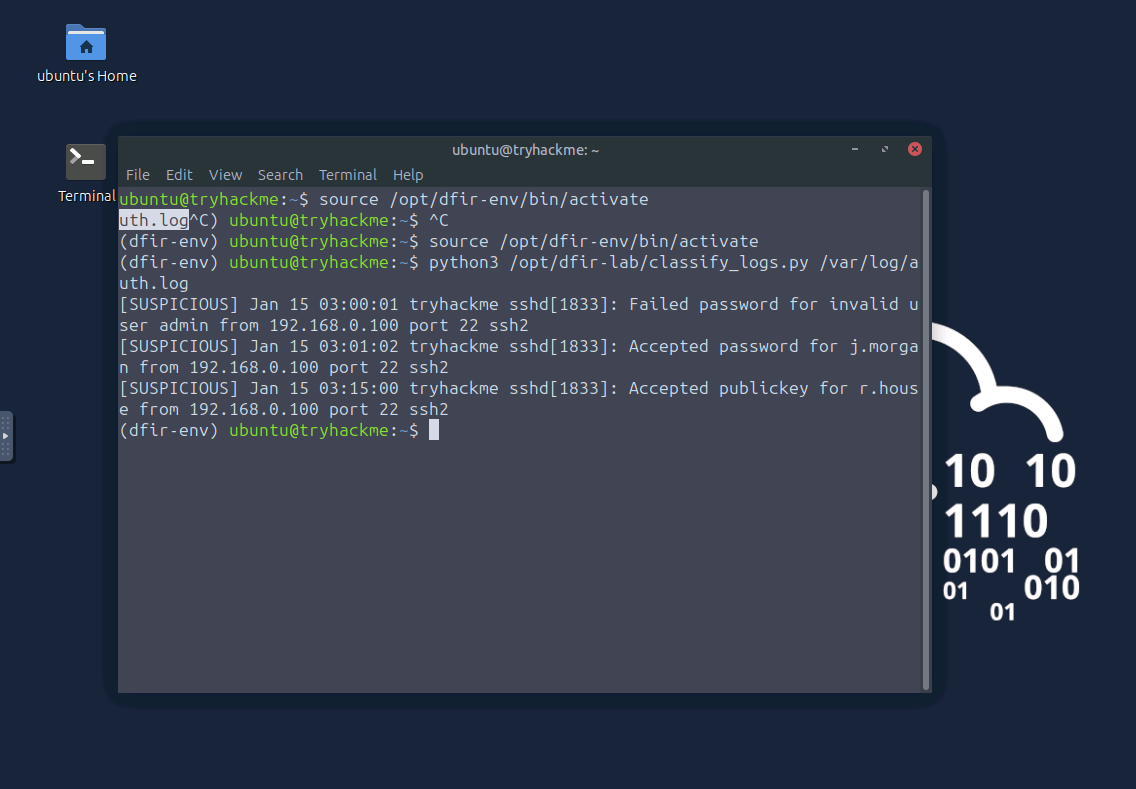
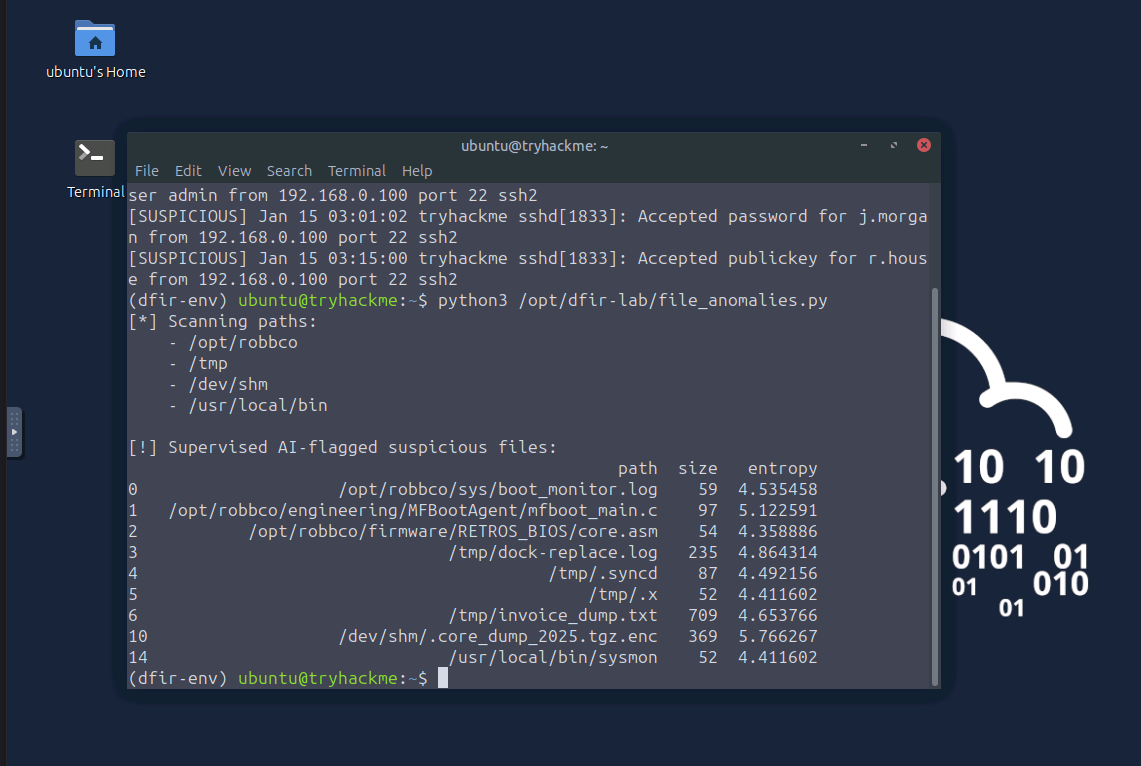
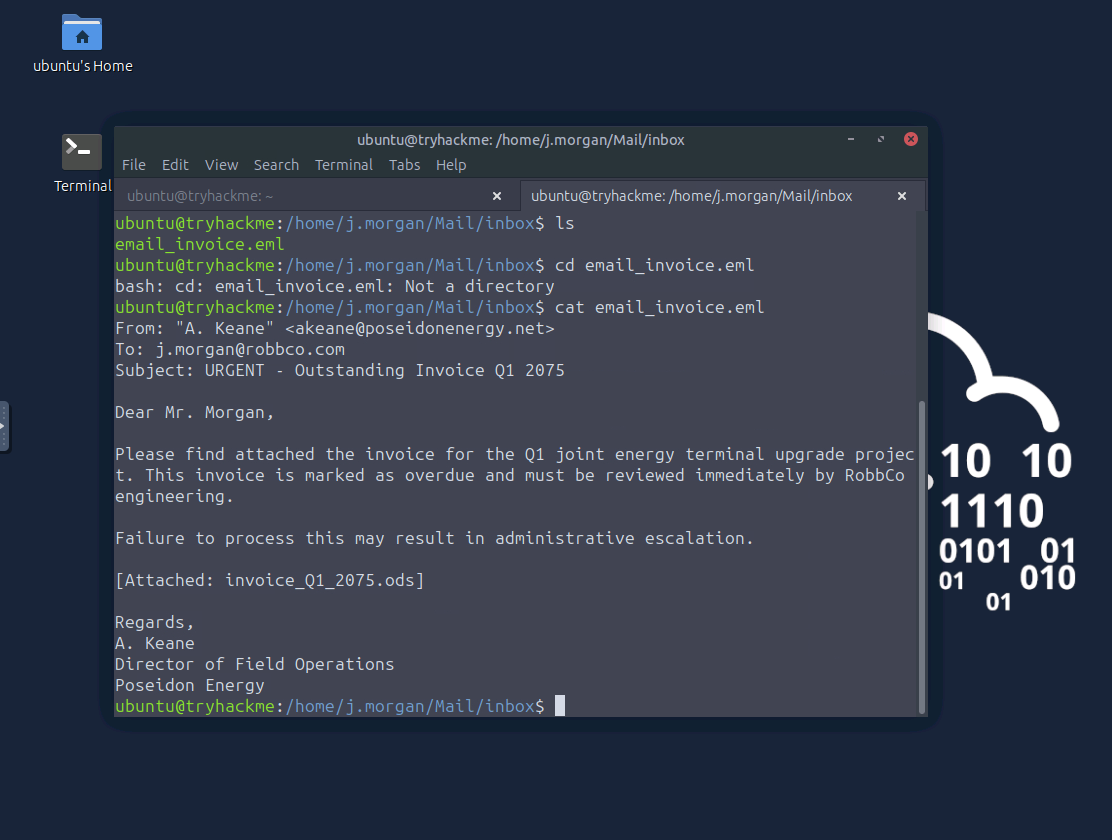
How to solve this task: Start the virtual environment (source /opt/dfir-env/bin/activate). Run python3 /opt/dfir-lab/classify_logs.py /var/log/auth.log to find the successful login time for j.morgan. Next, run python3 /opt/dfir-lab/file_anomalies.py to identify suspicious files. Investigating /tmp/invoice_dump.txt leads to the invoice_Q1_2075.ods phishing lure, and reading the related email reveals the attacker's email address. Checking j.morgan's bash history uncovers the sudo nano command used for privilege escalation. Finally, reviewing the flagged files shows the exfiltrated archive .core_dump_2025.tgz.enc hidden in shared memory.
Activating the isolated Python virtual environment for forensic analysis.
Running the classify_logs.py AI script to identify suspicious activity in auth.log.
Using file_anomalies.py to automatically flag suspicious files across high-priority directories.
Reading the phishing email in j.morgan's inbox that served as the initial attack vector.
At what time does the attacker successfully log in as j.morgan?
03:01:02
What attack method was used to gain initial access?
Phishing
Can you find the attacker's email address?
What command did the attacker run as j.morgan to gain access to the r.house account?
sudo nano /home/r.house/.ssh/authorized_keys
What is the full path of the archive used to steal RobbCo's source code?
/dev/shm/.core_dump_2025.tgz.enc
Task 6: Conclusion
The conclusion summarizes the room's core lessons, reinforcing that while AI is incredibly powerful for accelerating analysis, spotting patterns, and identifying malicious behavior, it is ultimately a guiding light. Human intuition, critical thinking, and validation remain absolutely essential in the DFIR landscape.
All done!
No answer needed
Thanks for reading. See you in the next lab.